14 Nov Why Managed Services Will Save You More Than Money
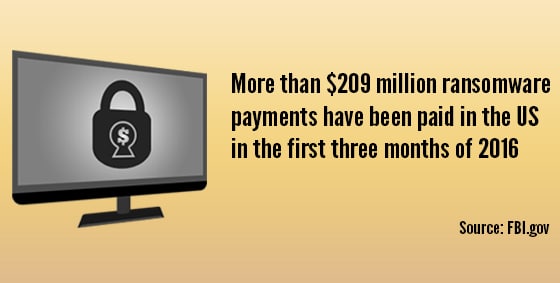
Why Managed Services Will Save You More Than Money “Downtime costs money.” That’s no secret, but it doesn’t quite capture the whole experience…you arrive to work in the morning, grab your coffee knowing you’ve got a hectic day ahead, and are ready to dive in. For some reason the computer can’t access the database and neither can anyone else’s. You restart the server while fielding calls left, right and center, but are unable to answer any client queries. Your hands are completely tied…and now the server is beeping furiously…what’s going on??! You’re not just in crisis mode, you’re on damage control as you call every tech you can think of, trying to find one who can come NOW. Not exactly the day you had planned. The Break/Fix Days Are Gone Previously, businesses only addressed their IT needs when something broke. A few hours down meant little in the scope of things. In today’s fast world, businesses rely heavily on IT and downtime just isn’t an option. Even the legalities of simply restoring financial, legal or medical files after a breach raises issues. How Can Managed Services Help? The cost of break/fix is now too high, both financially and emotionally. Simply put, your IT services are remotely monitored and proactively managed by a professional, external business. Your Managed Service Provider (MSP) runs regular diagnostics on equipment to identify impending failure and resolves problems before they happen. Benefits of Managed services Small to medium businesses in particular benefit from managed services, because they don’t usually have an on-site technician to oversee the multiple systems in use. By subscribing to a managed service provider, businesses can have reduced labor costs, access to a knowledge base, future-pacing, better data security and reduced downtime. Businesses can also know exactly what their upcoming costs are and plan accordingly. Read more about managed services Some of the managed services we can provide are: Remote support – This allows us to help you quickly without needing to be on-site Hardware monitoring – We monitor your servers and workstations to catch hardware failures before they happen. Managed anti-virus – We make sure your anti-virus is up to date and take immediate action if an infection occurs Patch management – We make sure your computer’s operating system is up to date, closing access to known vulnerabilities as soon as possible How much down time can your business afford? Call us at 570-235-1946 or visit our Contact Page...