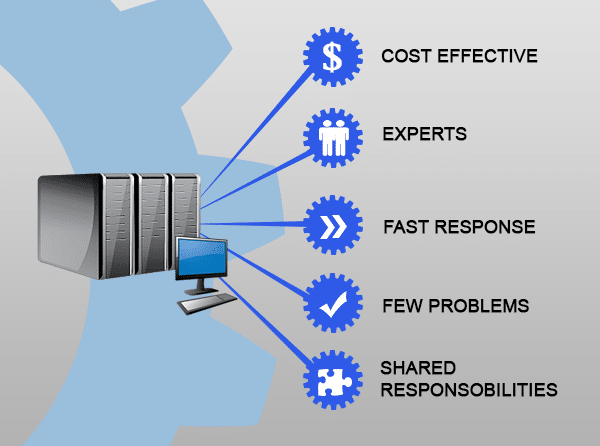
28 Jun 5 Ways Managed Services Can Grow Your Business
5 Ways Managed Services Can Grow Your Business Managed Service Providers (MSPs) can help grow your business with a proactive approach to managing their technology without the expensive step of hiring an in-house team. Your MSP is essentially a collection of niche technology experts working behind the scenes to keep your data safe, generate solutions to IT problems and keep your software updated. Even larger businesses who already have an IT person will often call in an MSP when daily support becomes overwhelming or a specific certification is required. Let’s explore 5 specific business breakthroughs an MSP can give you: It’s extremely cost-effective: There’s only so much in the budget for IT and responding to events on a break/fix basis will quickly exhaust your accounts. An MSP works by getting ahead of problems before they occur – making equipment last longer, defending against costly security breaches and keeping the business up and running. Instead of calling for a repair at a high hourly rate, you get a wide array of expert services for one predictable monthly fee. You have access to multiple experts: Businesses usually end up adding extra tasks to an unqualified but enthusiastic employee’s workload, resulting in costly problems. With MSPs, you have access to many people who are experts in very specific areas, and your existing staff can focus on tasks within their job description. Speedy problem resolution: Downtime and business don’t mix, so your MSP will provide a reliable expert on call (usually with 24/7 options) to troubleshoot and resolve any problems. Much of the time, you can also skip the delay of an on-site repair with rapid remote support available in just moments. Fewer problems: A large part of your MSPs service is fixing problems before they happen. While fixing things as they break isn’t the worst approach to IT management, it generally means you’re also suffering productivity losses, downtime and losing money by the second. Your MSPs primary goal is to ensure these problems are avoided completely, through system monitoring and robust security measures. They’ll also make sure every important software update and security patch is applied immediately, closing breach points and keeping your business safe. Shared responsibilities: As your business grows, so will your IT systems. A good MSP is on top of what your future needs will look like and knows which products and infrastructure are suitable to help you get there. Your MSP doesn’t just monitor your system and repair as required; they share responsibility for your system. This means measuring, reporting, analyzing and optimizing, working with you to introduce new technologies and processes. Depending on your level of contracted services, your MSP can actually become a catalyst for growth. Sounds good, doesn’t it? With managed services, your business always has the maximum security against threats, downtime and productivity drops. But for the savvy business owner, it’s also a way you can afford to leverage cutting-edge technologies, with complete peace of mind and ongoing support. Boost your business with managed services. Call us now at 570.235.1946 or visit our Contact Page...